Difference between revisions of "Privacy"
(→Projects: remove the crypto projects) |
(→Related news: We are Google employees. Google must drop Dragonfly) |
||
| Line 50: | Line 50: | ||
== Related news == | == Related news == | ||
| + | *2018-11-28: [https://medium.com/@googlersagainstdragonfly/we-are-google-employees-google-must-drop-dragonfly-4c8a30c5e5eb We are Google employees. Google must drop Dragonfly] | ||
*2018-09-05: [https://www.youtube.com/watch?v=eW-OMR-iWOE Ass Access] ''- Honest Government Ad, [https://boingboing.net/2018/09/04/illegal-math.html Oh FFS, not this again!]'' | *2018-09-05: [https://www.youtube.com/watch?v=eW-OMR-iWOE Ass Access] ''- Honest Government Ad, [https://boingboing.net/2018/09/04/illegal-math.html Oh FFS, not this again!]'' | ||
*2018-05-01: [https://signal.org/blog/looking-back-on-the-front/ Google and Amazon prove how shit they are when it comes to protecting user's privacy by making sure Signal can be censored again] | *2018-05-01: [https://signal.org/blog/looking-back-on-the-front/ Google and Amazon prove how shit they are when it comes to protecting user's privacy by making sure Signal can be censored again] | ||
Revision as of 00:02, 28 November 2018
Privacy is the resource that is made available by Security which in turn is a collection of tools for allowing information and resource to be made available only to selected people or groups. In OrganicDesign this means that our peer-to-peer network must have a good distributed encryption and authentication mechanism in place so that trust groups can contain private information securely and persistently even when none of the members are online.
Having very good encryption is important because these days more and more sensitive information needs to be stored in a robust distributed way while remaining fully private and under our own control. Examples of such information are passwords and private keys, scanned identification documents, personal correspondence and these days even digital money.
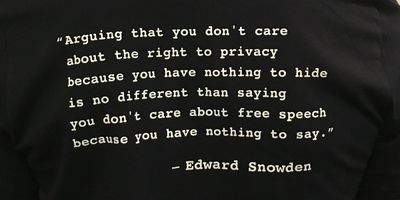
Many people believe that, if you have nothing to hide, there is nothing to fear from all this scrutiny. But if you resist the urge to pick your nose while others are present, or close the door when you go to the toilet, you are a privacy advocate. "When you realise that your whole life is under view," says the Tory MP David Davis, "it’s inhibiting." (from Can you disappear in surveillance Britain?). For more detailed information on this aspect of privacy, see Debunking a myth: If you have nothing to hide, you have nothing to fear.
| If you have something that you don't want anyone to know, maybe you shouldn't be doing it in the first place. | |
| — Eric Schmidt (CEO of Google) |
Contents
Real security a myth?
There isn't much confidence in real privacy these days with all the rumors and/or facts of "back doors" and quantum computers which can achieve seemingly miraculous computational power. But before getting sucked into all the hype, bear this simple foundation in mind - if two people share a private random block of information used one time only to encrypt a message of the same size, it is mathematically impossible to break, even by quantum computation - it is said to exhibit information theoretic security. It is only the level of organisation required amongst participants that currently makes this method impractical - in practice the network would usually combine this method with traditional methods.
Anonymous search
The DuckDuckGo search engine is a meta-search mechanism that gives the same results as Google, but is cleaner and preserves your privacy. It's a little slower to come up with results, but presents them in a nicer way and uses AJAX to maximise its usability.
Anonymous Internet browsing
Apart from the standard practice of using HTTPS connections when working with private content, it is also important to preserve anonymity - i.e. not giving away any information about the source of the web page requests. We use the Firefox browser with the TorButton add-on. There also another called FoxTor but I haven't tried that one yet. These solutions both use the TOR (The Onion Router) to achieve anonymity.
The add-on is easy enough to install, but I found that I also needed to apt-get install polipo and change the port settings in the TorButton preferences. The HTTP and SSL had to be changed from 8118 to 8123 and the SOCKS from 9050 to 4424. I found the ports that polipo was using with netstat -lp|grep polipo. After installation, you can check if it's working by switching it on and then checking your ip address and its estimated geographical location.
Another useful related addon to Firefox is the User Agent Switcher.
Private communications
- First Silent Circle, now private file transfer from phones
- PGP email
- Off-the-Record Messaging
- TOR chat
- Gliph - Secure Texting + Bitcoin Payments
- Telegram - cloud-based, heavily encrypted, free, open instant messaging
Projects
- Me and my shadow - take control of your data
- NoMoreGoogle.com - alternative privacy-aware apps
- RiseUp.net - another alternatives sites
- Cryptocat - open-source web-based private chat
- ZeroLink - very good looking Bitcoin mixer project
Silent Circle- Private comms of email, mobile, voip, IM and teleconferencing, by Dr. Zimmerman and others- Retroshare - Open Source cross-platform, private and secure decentralised communication platform. It lets you to securely chat and share files with your friends and family, using a web-of-trust to authenticate peers and OpenSSL to encrypt all communication. RetroShare provides filesharing, chat, messages, forums and channels
- Waterken
- GNU Privacy Guard (GPG) - GNU implementation of the OpenPGP standard
- StrongSwan - IPsec for Linux
- Onion Pi - TOR on Pi
- prism-break.org - stop reporting your online activities to the US government with these free alternatives to proprietary software
- Tails - Debian with onion, takeaway style!
- Private Internet Access (PIA) - VPN provider committed to privacy, no logging and excellent legal support
- Silent Vault - using voucher-safe to make bitcoin anonymous
- okTurtles + DNSChain - excellent project addressing issues with HTTPS and certificate authority fraud
- ZeroNet - decentralised websites using Bitcoin crypto and the BitTorrent network
- Rifle - more secure and efficient alternative to Tot and I2P underway at MIT
- MicroG - a libre software alternative to Android making good progress
Related news
- 2018-11-28: We are Google employees. Google must drop Dragonfly
- 2018-09-05: Ass Access - Honest Government Ad, Oh FFS, not this again!
- 2018-05-01: Google and Amazon prove how shit they are when it comes to protecting user's privacy by making sure Signal can be censored again
- 2017-09-18: W3C and Tim Berners-Lee go all fucked up and EFF resigns
- 2017-07-23: In Xinjiang, China, police have set up checkpoints to ensure that the government-mandated "Jingwang" spyware is installed
- 2017-04-27: Coalition Forms To Stop Trump Admin From Forcing Travellers To Give Up Passwords
- 2017-03-16: New Zealand Customs likely to get power to gain passwords
- 2017-03-10: WikiLeaks "Vault-7" press release
- 2017-01-20: Why Financial Privacy Is About More Than Using Bitcoin to Buy Drugs on the Internet
- 2016-10-26: TumbleBit - a mixing protocol that extends CoinSwap (paper, code)
- 2015-08-25: Bitcoin Privacy Tool "CoinShuffle" Sees First Transaction
- 2016-01-04: Dutch government backs strong encryption, condemns backdoors
- 2015-10-10: EFF: The Final Leaked TPP Text is All That We Feared
- 2015-02-26: Net Neutrality: Triumph of the Ruling Class
- 2015-02-13: Facebook's Name Policy Strikes Again, This Time at Native Americans
- 2015-01-13: End-to-end encryption ban on the table in UK
- 2014-12-23: The Tor Onion Is Under Attack and Rapidly Disintegrating
- 2014-11-19: Freedom Act Fails To Pass Senate
- 2014-11-14: 81% of Tor users can be de-anonymised by analysing router information, research indicates
- 2014-10-10: The Government’s War on Your Right to Encrypted Privacy
- 2014-10-01: Facebook sorry – almost – for secret psychological experiment on users
- 2014-09-28: FBI Blasts Apple, Google Phone Encryption: It "Allows People To Be Beyond The Law"
- 2014-09-14: The NSA and GCHQ Campaign Against German Satellite Companies - The Intercept
- 2014-08-27: Dark Wallet vs Bitcoin Fog: Battle Of Anonymous Bitcoin Services
- 2014-07-17: Censorship war: Website unmasks links Google is blocking from search results
- 2014-05-20: Latest leaks 'raises questions about NZ's surveillance'
- 2014-04-18: IRS awarded contract to surveillance company that tracks license plates
- 2013-12-19: Webcams can be covertly compromised by cops and hackers
- 2013-11-20: Inside America's Plan to Kill Online Privacy Rights Everywhere
- 2013-11-01: NSA Files: Decoded - what the revelations mean for you
- 2013-10-27: How one small American VPN company is trying to stand up for privacy
- 2013-10-27: "Self-censored UK media" frightened to show true outrage with global spying
- 2013-10-10: NSA has inserted its code into Android
- 2013-08-31: Privacy watch on Facebook's tagging moves - Facebook consideres new "suggest tag" feature
- 2013-08-21: How to Keep the NSA Out of Your Computer - sick of government spying, corporate monitoring, and overpriced ISPs? There's a cure for that
- 2013-08-20: Groklaw - forced exposure
- 2013-08-09: Lavabit email service abruptly shut down - founder of Lavabit said he would not be complicit in "crimes against the American people"
- 2013-08-14: Google: Gmail users "have no legitimate expectation of privacy"
- 2013-07-27: New Zealanders protest national security bill
- 2013-07-17: Yahoo wins lawsuit to declassify docs of proving resistance to PRISM
- 2013-07-15: Richard Stallman: Snowden leak a chance for privacy, time to fight
- 2012-08-05: If You See This Google Warning, Act Fast: Big Brother is Watching
- 2011-06-28: Microsoft patent allows for web-based spying technology
See also
- Security
- SSH hacks
- Day of reckoning for Tax Havens - Article from the Sunday Star Times on May 16, 2010
- Google Wi-Fi privacy row
- A paper trail of betrayal: Google's net neutrality collapse
- Wikipedia:Secret sharing
- Shamir's Secret Sharing - an algorithm for group privacy
- How a Lone Grad Student Scooped the Government and What It Means for Your Online Privacy
- Why Facebook's Facial Recognition is Creepy
- Cisco’s cloud vision: Mandatory, monetized, and killed at their discretion
- German 'Government' R2D2 Trojan FAQ
- Is Gravatar a privacy risk - why yes, yes it is!
- Anonymous Distros
- NSA black paper - excellent intro to online privacy for non-technical users
- Deploying perfect forward secrecy
- Duck Duck Go: Illusion of Privacy - some interesting comments at the bottom including one by DDG CEO
- An introduction to Tor vs I2P
- Nothing to hide argument
- Opt out from online behavioural advertising
- HiddenFromGoogle.com
- Edward Snowden: The Untold Story - WIRED
- Things That Can And Cannot Be Said - meeting between Arundhati Roy, John Cusack, Dan Ellsberg and Edward Snowden
- The attack that broke the Dark Web—and how Tor plans to fix it
- Eight Memorable Passages From Apple’s Fiery Response to the FBI
- The Crypto Anarchist Manifesto - Tim May, 1988
- A Cypherpunk's Manifesto - Eric Hughes, 1993
- Find out what Google and Facebook know about you