Difference between revisions of "Proof of agreement"
(→Signing the agreement: using electrum) |
(→Creating the agreement text: gov ID) |
||
| Line 40: | Line 40: | ||
0000000000000000000da391191dd04feefc62299cdfd89ca77c662836da422f | 0000000000000000000da391191dd04feefc62299cdfd89ca77c662836da422f | ||
</source> | </source> | ||
| + | |||
| + | Here I've used only my first name and associated myself only with my chosen online profile, but in a real agreement you would use your full name and a physical address and maybe the number of a government ID like a passport as well. | ||
== Getting the hash (fingerprint) of the agreement == | == Getting the hash (fingerprint) of the agreement == | ||
Revision as of 18:11, 4 August 2019
This article will cover a simple method using freely available tools for people to create an agreement amongst themselves which is digitally signed by all participants. The agreement is created in such as way that the identity of all participants, the authenticity of their signatures, and the time the agreement was signed can be verified by anyone. These verifications are very strong, but don't rely on any third-party authority and can be carried out by anyone using freely available tools without any specialised skills or knowledge.
Contents
Public key cryptography
Public key cryptography is the kind of system where the owner holds a secret private key that gives them ownership over the resource the key is protecting, and an associated public key which is safe to share publicly. Two popular example are PGP keys and Bitcoin addresses.
With PGP key pairs, anyone can use a public key to encrypt information knowing that only the person holding the private half of that key will be able to decrypt it. Also, the holder of the private key can sign messages resulting in a digital signature than anyone can verify using the public key. When someone sends a message they can sign it with their PGP key so that the recipient can use the sender's public key to ensure that the message was really sent by the holder of the private key.
In the case of Bitcoin, anyone can send money to any public bitcoin address, knowing that only the holder of the associated private key will be able to spend that money. As with PHP, the holder of the private key is also able to sign messages with it, and anyone can verify that the signature is valid using the public key.
Publicly associating yourself with a key
The first part to being able to create verifiable agreements between people, is being able to verify an irrefutable connection between a physical person and a public key they hold.
If you haven't already done so, you can publish any of your public keys either on your own site, or on a site that supports various forms of keys in user's profile information such as Keybase, OneName or some of the social networks such as Mastodon. For the purpose of creating a good agreement, it's a good idea to use a recognisable profile picture and include other details such as web site and email addresses in your profile.
This information may be solid at the time the agreement was made, but we want to make an agreement that can stand the test of time. The profile page you've chosen to use for the agreement may not be very permanent, for example the domain could expire, the company running the site go bankrupt or you may decide to delete your account and move to another platform.
A very useful tool to help us with this problem is the "Wayback Machine" at web.archive.org. This site has snapshots of billions of web pages at specific times to preserve the history of the web. And if by chance your profile does not exist in the Wayback Machine when you search for it, you will be given the option of adding it right then.
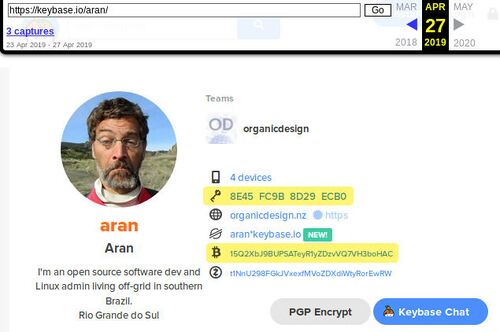
Here is a concrete example. I have a profile in a platform called KeyBase - or at least I did have at the time I wrote this! There were a few snapshots of my profile page already in the Wayback Machine when I checked just now, which you can see in the picture to the right, or by going there yourself.
This is a frozen snapshot of time, no matter what happens with Keybase in the future or what happens to my specific Keybase account, this snapshot will continue to exist in the Internet Archive which is supported by many organisations. You can see that this profile relates a number of things together; it has my name (full name would be better for this purpose) and photo, some of my web addresses and two public keys (highlighted). For most people there would also be provable connections with Facebook and Twitter etc, but I have deleted all such accounts out of my life!
You can also check the other related addresses for recent snapshots in the Wayback Machine, in this case we have organicdesign.pub/@aran (my Mastodon) which shows links back to my Keybase account and my blog, and my main site organicdesign.nz which shows links to the Mastodon and my Gitlab account. Using this tool also allows people to check how far back through time these various forms of identification go back.
So what we have here is a very strong connection between myself and a lot of known public activity and information about me, and this is all publicly and timelessly connected together along with three public keys that I control, a PGP key, a Bitcoin address and a ZCash address. Any of these keys could be used for the rest of the process which involves creating and signing the text of the agreement and using a blockchain to freeze a copy of these signatures in time. I'll show how it can be done with the PGP key and Bitcoin address.
Creating the agreement text
The agreement itself is something that only the participants can figure out, once they've arrived together at a definite statement that they all believe clearly describes what they're all in agreement on that's the first step in creating the text. For my example there will just be me as the only participant and a tiny fragment of text, but of course in reality there could be a number of participants and the text will be a whole document in the form of a PDF or something.
Aran agrees to buy a pizza for his wife if Bitcoin does not reach a new all time high in 2019.Here we see that the agreement text includes the names of all the participant(s) that will be signing, but we need to now include their profile URL that is known to exist in archive.org. You don't need to specify the archive.org URL in the agreement text, but it's important to know that a recent snapshot of it exists at the time the agreement is created.
Another important addition is to include the time, and the current Bitcoin block along with its hash - by including the block's hash, we're providing irrefutable proof that the agreement was not made before this block as created, because the block hash cannot possibly have been known in advance.
Our updated agreement has now been edited so that the identities of the participants includes their profile URL, and the time and block information is appended to the end.
Aran (keybase.io/aran) agrees to buy a pizza for his wife if Bitcoin does not reach a new all time high in 2019.
This agreement was created at 00:10, 2019-08-04 UTC, the Bitcoin block number was 588492 with a hash of
0000000000000000000da391191dd04feefc62299cdfd89ca77c662836da422fHere I've used only my first name and associated myself only with my chosen online profile, but in a real agreement you would use your full name and a physical address and maybe the number of a government ID like a passport as well.
Getting the hash (fingerprint) of the agreement
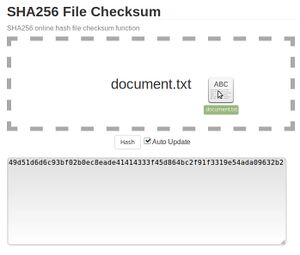
The next step is to get the hash of the agreement, which is a unique fingerprint that matches the exact agreement text. Remember that from this point on the agreement text cannot be changed, even if you see a typo or problem, otherwise the entire rest of the process will need to be repeated again. We'll use SHA-256 hashes because those are currently the most popular throughout the crypto world. You can do this using an online tool such as this one where you can simply drop the file on the page to get the hash as shown in the image to the right, or if you're using Linux or Mac you can do it on the command line as follows (you'll need to know the path and filename of your agreement document).
sha256sum /path/to/document.pdfIn my case the SHA-256 hash of my agreement is:
49d51d6d6c93bf02b0ec8eade41414333f45d864bc2f91f3319e54ada09632b2Signing the agreement

Only the holder of the private half of a key-pair can sign anything with their private key, and it's not something they might inadvertently do like accidentally clicking "I agree" or opening a file with a virus in it. A digital signature is a long sequence of letters and numbers that looks just like a hash, but if someone knows that it a signature and they also have the message it is signing and the public key that the message was signed with, then they can easily prove for themselves whether or not the signature really was signed by the key holder and corresponds to that exact message. In general it's easier to sign the message's hash rather than the message itself, especially if it's large. This avoids common mistakes like accidentally adding or removing spacing or newlines from the beginning or end of the document text which would lead to a completely different signature.
Digitally signing is not a difficult process, but it cannot be done with online tools because that would be a serious security risk since it needs to be done using your private key which should never be shared. In the popular electrum wallet signing a message is done from the tools menu, which opens the simple window shown on the right where you simple enter you message (or it's hash in our case) and the address you want to use the associated private key from. You then click "sign" and the digital signature code will be created for you. Note that you can also use this same window for verifying signatures. the signature for our message is as follows (note that I'm using a different address than the one shown in my for this example, but in reality it's very important that you use the same address).
HFodpjwKOps5B51ClBlh6/xsdu50nHSz1JBZnP0L1v2NU5vm+075sO9OlSkQ+9YFrspF3Hxs0kEMEQkZF3SvhgY=Recording the signing in the blockchain
Documenting the agreement
Verification
Verifying the authenticity of the participants
Verifying the signatures
Bitcoin: in your wallet, or using an online tool such as this one. PGP: